HIPAA-compliant messaging vs consumer apps is not a theoretical debate. HHS OCR recorded 725 large healthcare data breaches in 2024, the third consecutive year that breach totals have exceeded 700 (HIPAA Journal, 2025). Consumer messaging applications — apps designed for social contact, not clinical governance — appear repeatedly across the underlying incident reports as undocumented channels carrying protected health information (PHI) with no Business Associate Agreement (BAA), no audit trail, and no defensible access control. For physicians, compliance officers, and practice administrators evaluating HIPAA-compliant messaging vs consumer apps, the question is no longer whether these tools create liability. The enforcement record answers that. The question now is what a compliant replacement actually requires, and why the architecture of a consumer app cannot be retrofitted to meet those requirements.
ClinicianCore operates as a secure, HIPAA-compliant unified clinical communication platform built exclusively for physicians. The HCO (HealthCare Organization) module was built specifically to address the intra-office communication gap the physician texting the front desk about a Schedule II renewal, the nurse messaging the billing team about a diagnosis code, the administrator forwarding a patient’s insurance number over a group chat. These are the exact workflows that consumer apps absorb by default and that HIPAA’s technical safeguards govern without exception.
This article examines what the 2024-2025 HHS OCR enforcement record documents, what 45 CFR §164.312 actually mandates for electronic messaging, why consumer applications cannot satisfy those mandates by design, and what a HIPAA-compliant clinical communication architecture must include.
Key Takeaways
- The debate over HIPAA-compliant messaging vs consumer apps has a clear answer in the enforcement record: HHS OCR recorded 725 large healthcare data breaches in 2024, the third straight year above 700, an average of roughly two a day (HIPAA Journal, 2025).
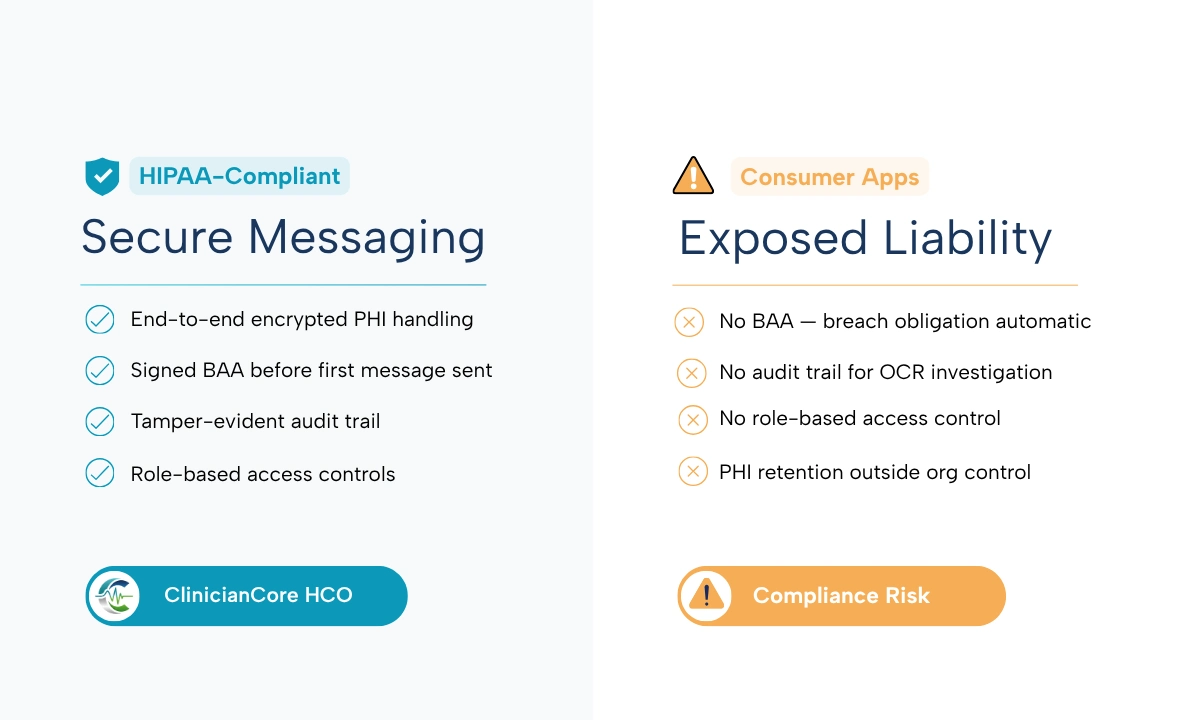
- Consumer messaging apps — including standard SMS, WhatsApp, and iMessage — lack the access controls, tamper-evident audit trails, and encryption specifications required by the HIPAA Security Rule (45 CFR §164.312).
- No Business Associate Agreement (BAA) exists between consumer app vendors and healthcare organizations. Without a signed BAA, any PHI transmitted through those channels creates an automatic breach obligation.
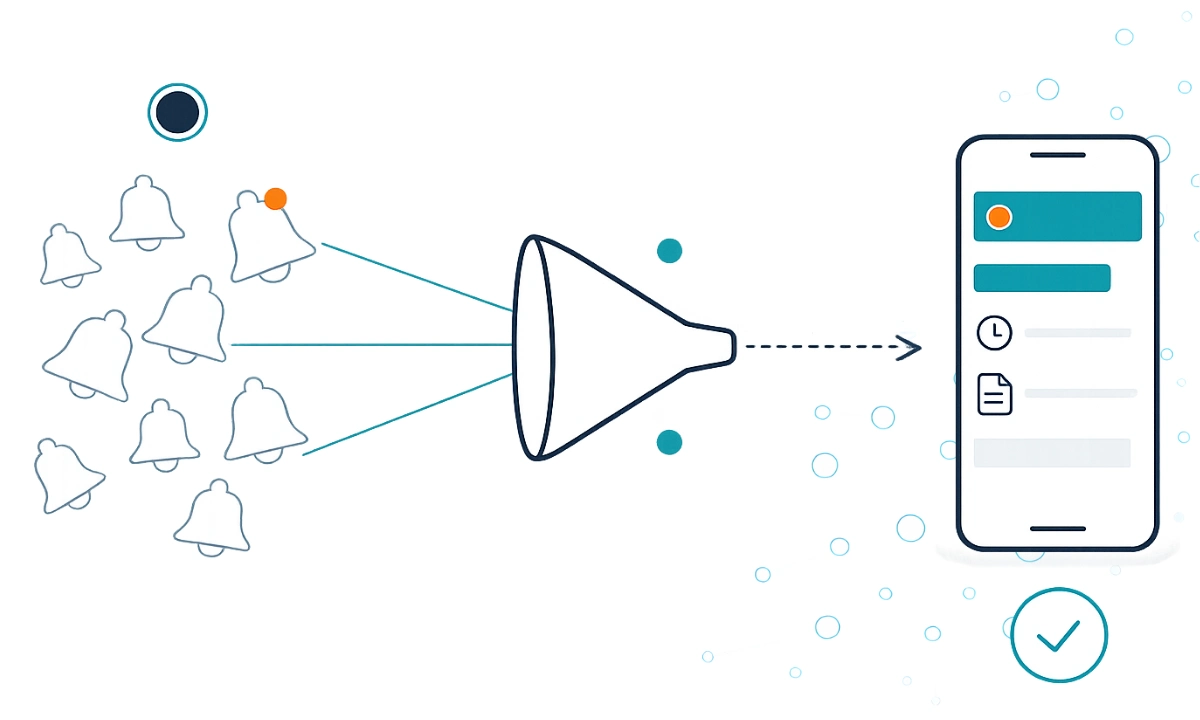
- Shadow IT in clinical settings refers specifically to undocumented communication channels used to transmit PHI outside approved systems. Physician-to-front-desk texting is the most common HCO exposure vector.
- ClinicianCore HCO replaces all consumer app communication with a HIPAA-compliant channel that signs a BAA, maintains tamper-evident audit logs, and gives compliance officers full governance visibility. Explore the HIPAA-compliant collaboration platform.
“Consumer apps were not built to carry PHI. The absence of a Business Associate Agreement is not a paperwork gap. It is a structural breach obligation waiting to be triggered. Every physician practice using WhatsApp or standard SMS for internal communication is one OCR audit away from discovering that convenience has a compliance price.”
 Neeraj Jain CEO & Co-Founder, ClinicianCore · Healthcare Technology Executive
Neeraj Jain CEO & Co-Founder, ClinicianCore · Healthcare Technology Executive
What HIPAA Requires from Clinical Messaging
HIPAA does not prohibit electronic messaging between clinical team members. It mandates specific technical safeguards that must govern any messaging system that carries PHI. Those safeguards are codified in the HIPAA Security Rule, 45 CFR §164.312, under the Technical Safeguards standard. Five requirements are directly relevant to clinical messaging:
- Access controls (§164.312(a)(1)): Unique user identification is mandatory. Every individual accessing PHI through any messaging channel must be authenticated with credentials assigned to that individual alone. Shared logins, shared devices without session-level authentication, and group accounts do not satisfy this standard.
- Audit controls (§164.312(b)): The covered entity must implement hardware, software, or procedural mechanisms to record and examine activity in systems that contain or use PHI. This means every message sent, received, forwarded, or deleted must be logged in a tamper-evident record tied to an authenticated user identity.
- Integrity controls (§164.312(c)(1)): The covered entity must implement policies and procedures to protect PHI from improper alteration or destruction. Messages must arrive exactly as sent, without modification in transit, and must be retainable in their original form.
- Transmission security (§164.312(e)(1)): Technical security measures must guard against unauthorized access to PHI transmitted over electronic communications networks. Encryption is the standard-of-practice implementation and, while formally an addressable specification rather than required implementation, the HHS guidance makes clear that failure to encrypt requires a documented alternative of equivalent protection.
- Business Associate Agreement (§164.308(b)(1)): Any vendor whose service handles PHI on behalf of a covered entity is a Business Associate under HIPAA. In the HIPAA-compliant messaging vs consumer apps comparison, a signed BAA is the single fastest disqualifying test: if the vendor will not sign one, the platform fails before any other evaluation begins.
None of these requirements are interpretable as suggestions. They are the minimum floor for any clinical communication system. A messaging application that cannot satisfy all five does not qualify as HIPAA-compliant, regardless of what its marketing materials state.
Why Consumer Apps Cannot Comply by Design
The core issue in HIPAA compliant messaging vs consumer apps is not configuration. Standard SMS, WhatsApp, and iMessage are non-compliant because their architecture was designed for a different purpose, and that architecture cannot be modified from the user side to meet 45 CFR §164.312.
Access Controls
Consumer apps authenticate to a phone number or a personal Apple ID, not to a role-based healthcare identity. When a physician uses a personal device, access control is the device passcode: a control that does not distinguish between the physician, a family member who borrows the phone, and a thief. There is no centrally issued unique identifier per 45 CFR §164.312(a)(1). There is no session timeout. Role-based access, meaning the ability to restrict what a front desk coordinator can see versus what a prescribing physician can see, does not exist.
Audit Controls
Consumer apps do not generate tamper-evident audit logs readable by a compliance officer. Message history exists on the user’s device and, in some cases, on the vendor’s servers. But that history is not attributable at the individual user level in a format that satisfies an OCR audit request. If a breach involves a message sent over a consumer app, the covered entity cannot produce the audit record that 45 CFR §164.312(b) requires. The breach notification obligation exists, but the evidence of safeguards does not.
Transmission Security and Encryption
WhatsApp applies end-to-end encryption to message content in transit between two devices. That encryption, however, is controlled by the app vendor’s key infrastructure, not the healthcare organization’s. The covered entity does not hold encryption keys, cannot verify key management practices, and cannot demonstrate compliance with its own policies. Standard SMS carries no encryption in transit at all. iMessage encrypts between Apple devices on iMessage protocol but reverts to unencrypted SMS when the recipient is on a non-Apple device, creating a transmission security gap that the sender cannot reliably detect.
More fundamentally: WhatsApp does not sign a Business Associate Agreement. Neither does Apple for iMessage. Neither does any standard SMS carrier in the context of clinical PHI transmission. Without a BAA, the transmission of PHI through any of these channels represents an impermissible disclosure under 45 CFR §164.402, triggering breach notification requirements regardless of whether the message was intercepted by an unauthorized party. The HHS Office for Civil Rights has been explicit on this point in its guidance on online tracking technologies and PHI (HHS OCR, 2024).
Message Retention and Deletion
HIPAA requires that PHI be retainable in its original form and protectable from improper destruction. Consumer apps store messages on personal devices and on vendor-controlled cloud infrastructure. Both are outside the covered entity’s control. If a physician leaves a practice, the messages on their personal device leave with them. If an employee deletes a message thread, no tamper-evident record remains. If a vendor modifies or deletes messages pursuant to their own terms of service, the covered entity has no recourse and no audit trail showing what happened.
The 2024-2025 HHS OCR Enforcement Record
The real-world cost of ignoring HIPAA-compliant messaging vs consumer apps distinctions is documented in OCR’s enforcement actions across 2024 and 2025. In 2024, OCR closed 22 investigations with financial penalties, collecting $12,841,796 in civil money penalties and settlements (HIPAA Journal, 2025). Enforcement actions in 2025 increased to 21 penalties. The most commonly identified violations across enforcement actions are risk analysis failures and failures to implement the technical safeguards of 45 CFR §164.312.
Several specific patterns in the enforcement record are directly relevant to clinical messaging practices:
Impermissible Disclosures Through Undocumented Channels
OCR resolution agreements consistently identify impermissible disclosure of PHI as a core violation element. When PHI is transmitted over a channel with no BAA — which is the structural condition of every consumer messaging app — every transmission involving PHI is a potential impermissible disclosure. The covered entity bears the burden of demonstrating that an alternative safeguard of equivalent strength was in place. Without a BAA and without audit logs, that burden cannot be met.
Risk Analysis Failures
Risk analysis is the single most commonly cited HIPAA violation in OCR enforcement actions. Under 45 CFR §164.308(a)(1), covered entities must conduct an accurate and thorough assessment of the potential risks and vulnerabilities to ePHI. A risk analysis that fails to identify consumer messaging apps used by staff as an ePHI risk vector is facially incomplete. If a staff member is texting PHI over a consumer app and that practice is not documented in the risk analysis and risk management plan, the covered entity is out of compliance on two counts simultaneously.
The Change Healthcare Context
The 2024 Change Healthcare ransomware attack exposed the protected health information of an estimated 192.7 million individuals, the largest healthcare data breach on record (HIPAA Journal, 2025). While that incident involved a different attack vector, its scale triggered a significant increase in compliance scrutiny across the industry. Organizations that had deprioritized messaging security as a secondary concern found themselves in the middle of an enforcement environment that is examining their full ePHI governance posture, not just their cybersecurity perimeter.
Shadow IT: The Specific HCO Risk in Physician Practices
Shadow IT, in the context of healthcare organizations, refers to information technology used by staff to perform work functions without the knowledge, approval, or governance of the compliance and IT function.
Consumer messaging apps are the most prevalent form of shadow IT in physician practices, and they sit at the center of the HIPAA-compliant messaging vs consumer apps risk profile for intra-office clinical communication.
Consider the transaction types that make HIPAA-compliant messaging vs consumer apps a daily operational question in a typical 10-15 physician practice:
- Physician to front desk: refill authorization for a Schedule II medication, referral instructions with patient name and diagnosis, scheduling request citing a clinical reason
- Physician to nurse: pre-procedure instruction with patient identifier, medication dose adjustment with patient name attached
- Nurse to billing team: diagnosis code correction attached to a patient visit record
- Practice administrator to physician: insurance pre-authorization status with patient information
Each of these message types contains PHI as defined in 45 CFR §160.103. Each one, if transmitted over a consumer app, constitutes a potential HIPAA violation. The clinical team is not acting with malicious intent. They are using the most convenient tool available. The problem is that convenience and compliance are structurally incompatible with consumer app architecture.
Approximately 80% of medical professionals now use personal mobile devices for work communication (HIPAA Guide, 2025). BYOD policies, when not accompanied by a HIPAA-compliant messaging platform, convert that statistic directly into organizational liability. ClinicianCore’s end-to-end encryption for healthcare administrators covers the governance structure required to address BYOD risk without eliminating the flexibility that clinical teams depend on.
The shadow IT risk is compounded by the absence of an audit trail. When OCR audits a covered entity, investigators request access controls documentation, workforce training records, and evidence that PHI access was limited to authorized individuals. A covered entity whose staff communicated over consumer apps cannot produce this documentation. The operational record of that communication exists only on personal devices, outside the covered entity’s control.
The BAA Requirement: Why It Is the Threshold Test
The Business Associate Agreement is the single fastest test for whether a messaging platform qualifies as HIPAA-compliant. Under 45 CFR §164.308(b)(1), a covered entity may not disclose PHI to a business associate unless the covered entity has obtained satisfactory assurances that the business associate will appropriately safeguard the information. Those assurances must be documented in a written BAA.
WhatsApp does not offer a BAA to healthcare organizations. iMessage does not offer a BAA. Standard SMS carriers do not sign BAAs in the context of clinical PHI transmission. The HIPAA Journal (2026) confirms this directly: a vendor’s willingness to sign a BAA is the minimum threshold test for HIPAA compliance, and consumer app vendors do not pass that test.
The practical implication for any HIPAA compliant messaging vs consumer apps evaluation is significant: even if a consumer app’s encryption were technically adequate and every staff member were trained on minimum necessary standards, the absence of a BAA makes every PHI-containing message an impermissible disclosure. The BAA is not a formality. It is the legal foundation for the entire compliance relationship with any messaging vendor.
The HIPAA compliant collaboration platform provided by ClinicianCore signs a BAA as a standard component of the onboarding process. No additional legal negotiation is required. The BAA is executed before the first message is sent, and it governs every communication channel within the platform.
For a detailed breakdown of what the platform architecture requires beyond the BAA, see: what makes a platform truly HIPAA compliant.
What a HIPAA-Compliant Clinical Messaging Architecture Requires
Understanding HIPAA compliant messaging vs consumer apps begins with what a compliant platform must actually satisfy. These are not vendor features. They are compliance requirements drawn directly from 45 CFR §164.312 and the HIPAA Security Rule.
Signed Business Associate Agreement
The vendor executes a BAA before PHI enters their infrastructure. The BAA documents the vendor’s compliance obligations, the permitted uses of PHI, and the breach notification requirements that apply to the vendor as a Business Associate.
Role-Based Access Controls
Access to PHI within the messaging system is restricted by job role. A front desk coordinator does not have access to messages between a prescribing physician and a specialist. A billing team member does not have access to clinical discussion threads. Access is controlled by the system, not by social convention.
Tamper-Evident Audit Trails
Every message action — sent, received, read, forwarded, deleted — generates a log entry tied to an authenticated individual identity. The audit trail cannot be modified by end users. The compliance officer has read access to audit logs without requiring IT intervention for individual queries.
End-to-End Encryption
Message content is encrypted in transit and at rest. The encryption keys are held under the healthcare organization’s governance model, not the vendor’s. The vendor cannot read message content.
Remote Wipe and Device Management
If a device containing PHI is lost or stolen, or if a staff member leaves the organization, the covered entity must be able to remotely remove PHI from that device or revoke access to the messaging system. Consumer apps on personal devices cannot be remotely managed by the healthcare organization.
Message Retention and Legal Hold
Messages are retained in accordance with the applicable state medical records retention requirements, typically seven to ten years. The system supports legal hold, meaning specific message records can be preserved and protected from deletion during litigation or investigation.
These six requirements map directly to the technical and administrative safeguards of the HIPAA Security Rule. A platform that satisfies all six eliminates the structural exposure that consumer apps create. A platform that satisfies five does not.
How ClinicianCore HCO Helps: HIPAA Compliance
How ClinicianCore HCO Helps: HIPAA Compliance
The ClinicianCore HCO module replaces consumer app communication with a HIPAA-compliant channel that signs a BAA, maintains tamper-evident audit trails, and gives compliance officers full governance visibility across every intra-office communication thread. Every message is encrypted end-to-end, every access event is logged to an authenticated user identity, and role-based permissions ensure that PHI reaches only the team members authorized to receive it. ClinicianCore operates as a secure, HIPAA-compliant unified clinical communication platform built exclusively for physicians — making HIPAA-compliant intra-office communication the operational default, not an add-on policy requirement.
Learn more: HealthCare Organization (HCO) | HIPAA Compliant Communication Platform | HIPAA compliant collaboration platform
HIPAA Compliant Messaging vs Consumer Apps: The Enforcement Case for Switching
The 2024-2025 HHS OCR enforcement record does not leave room for ambiguity about the risk consumer messaging apps create in clinical settings. Seven hundred twenty-five large healthcare data breaches in 2024. Twenty-two enforcement actions with financial penalties. Risk analysis failures and technical safeguard violations as the most common findings. This is not a theoretical compliance concern.
When evaluating HIPAA compliant messaging vs consumer apps, the structural gaps are not debatable. Practices using standard SMS, WhatsApp, or iMessage operate with no BAA, no tamper-evident audit trail, no role-based access control, and no message retention governance. Each of those gaps is independently auditable and independently penalizable.
A compliant replacement is available. ClinicianCore operates as a secure, HIPAA-compliant unified clinical communication platform built exclusively for physicians, with the HCO module designed specifically to close the intra-office communication gap that consumer apps currently occupy. The platform signs a BAA, maintains tamper-evident audit logs, provides role-based access, and encrypts every message end-to-end. The enforcement record makes the argument for migration. ClinicianCore HCO provides the architecture.
Frequently Asked Questions
Does using WhatsApp for clinical communication violate HIPAA?
Using WhatsApp to transmit PHI in clinical communication violates HIPAA because WhatsApp does not sign a Business Associate Agreement with healthcare organizations. Under 45 CFR §164.308(b)(1), any message containing PHI sent over a platform with no BAA constitutes an impermissible disclosure, triggering mandatory breach notification regardless of interception. ClinicianCore HCO eliminates this exposure by operating under a signed BAA.
What does HIPAA require from a clinical messaging platform?
HIPAA requires clinical messaging platforms to satisfy five technical safeguards under 45 CFR §164.312: unique user access controls, tamper-evident audit controls, message integrity protections, transmission encryption, and a signed Business Associate Agreement with the platform vendor. Platforms that cannot satisfy all five do not qualify as HIPAA-compliant. ClinicianCore HCO meets each requirement by design.
What is a Business Associate Agreement and do I need one for clinical messaging?
A Business Associate Agreement (BAA) is a written contract required by 45 CFR §164.308(b)(1) between a covered entity and any vendor that handles PHI on its behalf. For clinical messaging, any platform transmitting PHI through its infrastructure must have a signed BAA in place before any message is sent. Without it, every PHI-containing message is an impermissible disclosure under HIPAA.
What did the HHS OCR enforcement record document about HIPAA violations in 2024-2025?
HHS OCR closed 22 investigations with financial penalties in 2024, collecting $12,841,796 in civil money penalties and settlements. Enforcement increased in 2025 with 21 penalties imposed. The most commonly identified violations involve risk analysis failures under 45 CFR §164.308(a)(1) and failures to implement the technical safeguards of the HIPAA Security Rule, including access controls and audit controls.
How does ClinicianCore HCO eliminate shadow IT risk in physician practices?
ClinicianCore HCO eliminates shadow IT risk by replacing the convenience gap that drives consumer app adoption. It provides a secure, HIPAA-compliant unified clinical communication platform built exclusively for physicians with the same immediacy as consumer messaging, so staff have no operational reason to route PHI through unapproved channels. Role-based access, BAA, and tamper-evident audit trails govern every message sent within the platform.
References
- HHS Office for Civil Rights (2025). Resolution Agreements and Civil Money Penalties.https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/agreements/
- HIPAA Journal (2025). 2024 Healthcare Data Breach Report. https://www.hipaajournal.com/2024-healthcare-data-breach-report/
- HIPAA Journal (2026). Healthcare Data Breach Statistics — Updated for 2026.https://www.hipaajournal.com/healthcare-data-breach-statistics/
- HIPAA Journal (2026). Is Texting in Violation of HIPAA? 2026 Update. https://www.hipaajournal.com/texting-violation-hipaa/
- HIPAA Journal (2026). 2025 Healthcare Data Breach Report. https://www.hipaajournal.com/2025-healthcare-data-breach-report/
- HHS Office for Civil Rights (2024). Guidance on Online Tracking Technologies and the HIPAA Rules.https://www.hhs.gov/hipaa/for-professionals/privacy/guidance/hipaa-online-tracking/index.html
- U.S. Department of Health and Human Services. HIPAA Security Rule, 45 CFR §164.312 — Technical Safeguards.https://www.hhs.gov/hipaa/for-professionals/security/laws-regulations/index.html
- U.S. Department of Health and Human Services. HIPAA Privacy Rule, 45 CFR §164.402 — Definition of Breach.https://www.hhs.gov/hipaa/index.html
- HIPAA Guide (2025). What are the HIPAA Rules Regarding Text Messaging? https://www.hipaaguide.net/hipaa-rules-regarding-text-messaging/
- American Hospital Association (2025). 2025 Cybersecurity Year in Review — Breaches and Defensive Measures.https://www.aha.org/news/aha-cyber-intel/2025-10-07-2025-cybersecurity-year-review-part-one-breaches-and-defensive-measures